What is Workflow Automation?
Workflow automation replaces time-consuming manual tasks with software designed to execute many daily business processes automatically. Network administration, business operations and DevOps collaboration can be streamlined, resulting in cost-savings benefits for most organizations while reducing human error and processing time. Workflow automation improves communications and facilitates optimal use of employee time and company resources. Workflow inefficiencies and oversights can be eliminated by automating workflows.
10 Benefits of Workflow Automation
What Is Network Security Workflow Automation?
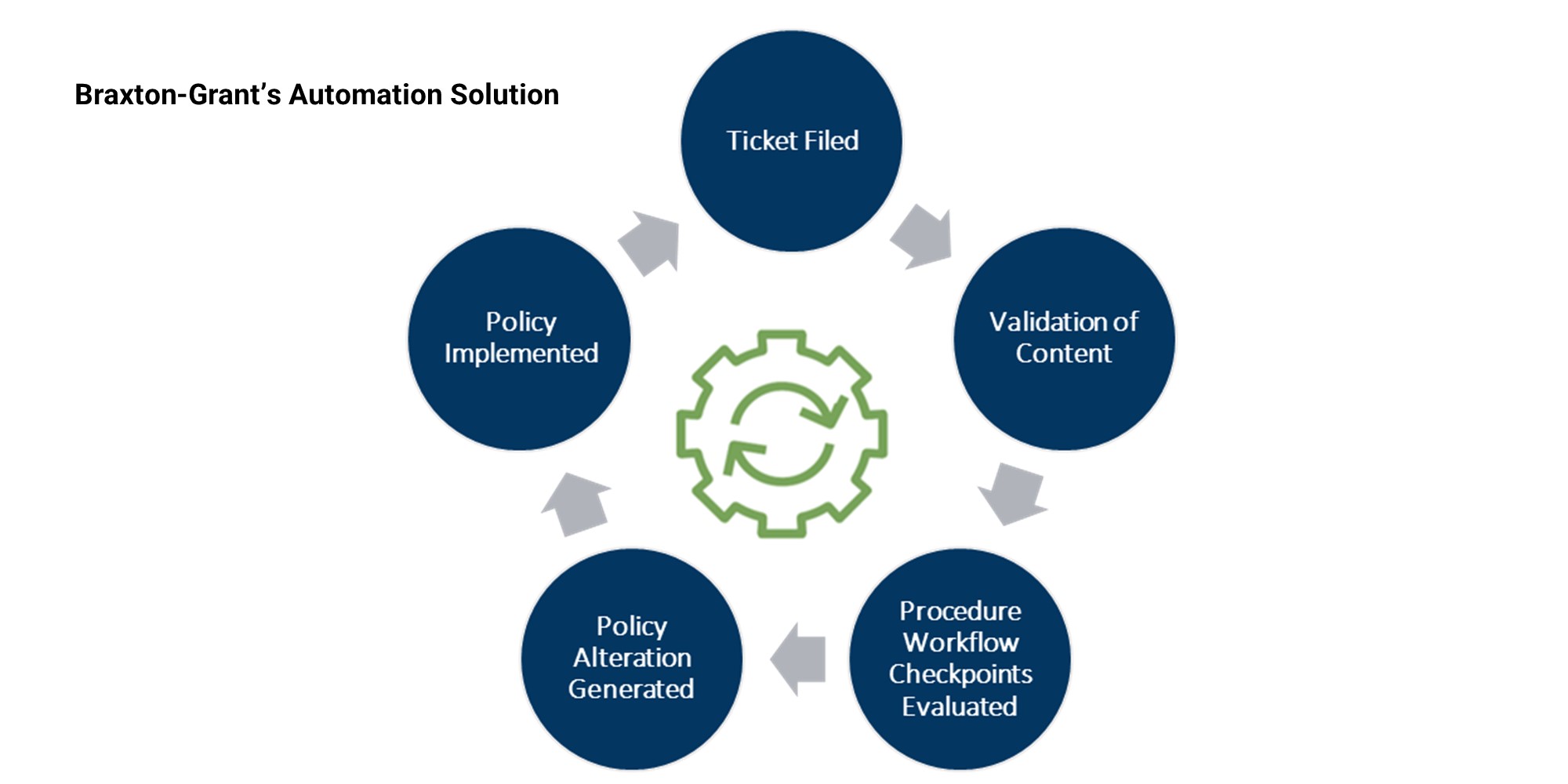
NEW! Solve Real Problems and Improve Efficiency with Network Security Automation Integration Developed by Braxton-Grant
The critical skill shortage of cybersecurity professionals today requires the development of new processes to make existing cybersecurity teams more efficient. The risk of burn-out and simply overwhelming staff with cumbersome daily tasks is a substantial issue for companies. Using an unprecedented approach developed by Braxton-Grant, common security tasks can be automated to be accomplished during normal business hours or on a custom schedule.
Braxton-Grant Technologies curated a groundbreaking integration capability solution between CA Automic Automation and API capable network security products. Our cyber engineers leverage certified knowledge and the open API offered by a variety of vendor cybersecurity tools to bring Workflow Automation to cybersecurity that has never been seen before. We can now expand workflow automation across any security tool with a RESTful API capability.
Examples of Automated Network Security Policy Tasks:
Network Automation promotes efficiency by reducing manual errors and employee workload, and improves security initiative delivery.
How does Braxton-Grant help?
As a trusted IT advisor, we create the best solutions for you no matter where you are in the process of adding Automation to your security environment. Every company can simplify business operations with Workflow Automation and Network Security Automation to keep up with the modern workplace and maximize resources. We are here to implement quickly and identify and resolve hidden gaps in your network.
Where are you in the Process of Adding Workflow Automation?
Our Vendor Partners
The way you do business is unique to you, and your security existence should reflect that. No matter where you are in the world or whether you have employees on-premises, hybrid, or remote, we work with a variety of partners so we can apply the best products and solutions for you.